The construction industry is digitizing at a breakneck pace, but this evolution has inviteda surge incyberattacks. While major firms often have robust internal defenses, they are only as strong as their weakest link.
 Over the next five years, businesses are expected to lose approximately $5 trillion as a result of cybercrime.
Over the next five years, businesses are expected to lose approximately $5 trillion as a result of cybercrime.
However, this type of setback isn't limited to hacking or massive data breaches. Something as simple as an email can lead to adverse consequences if proper care isn't used.
Not sure where to start? Don’t worry, we’ve got you covered!
Let’s take a look at everything you need to know about how to prepare for phishing emails in your cyber security protocol.
Ever got an email out of nowhere that says you've won something? Or how about that there's an urgent issue with your bank account?
The vast majority (if not all) of the time, these are scams that aim to get info like your account number, passwords, social security number, etc.
'Phishing' is a term derived from 'fishing' in reference to casting out your line (the emails) in search of a catch (personal information or sensitive data). Unfortunately, it's not always easy to undo the consequences if you fall for this trick.
There are plenty of telltale signs to watch out for if you receive a suspicious email.
Let's dive into some of the most common.
Example of an actual phishing email:
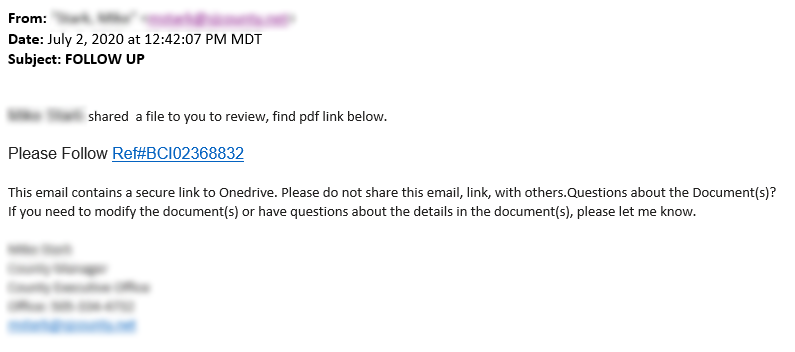
A couple things to take note of about this phishing email:
This tip isn't always applicable, but it can often be supporting evidence when there are other areas of concern in the suspected email.
Since these messages are sent en masse to thousands of people, they often won't include a name. They'll use general terms like 'customer', 'user', etc.
Phishing emails complete their data harvest by redirecting victims to a false web page that looks like a legitimate site they trust. From here, the recipients are asked to 'update their password' or perform a similar action that involves them inputting sensitive information.
Attachments may result in your computer becoming infected with a virus. This can prove to be exceptionally dangerous, as many viruses don't show obvious signs that an infection is present.
It's extremely unlikely for there to by any sort of grammar error in an official email from a reputable website. And, if there is, it's usually something minor.
In phishing emails, though, the copy often reads like it was written by someone who isn't fluent in English. This is one of the easiest ways to spot that something's not right.
Luckily, this is the easy part.
If you aren't sure if you're being scammed or not (some emails can be more on the convincing side), go to the website on your own through your browser. You shouldn't click a suspicious link under any circumstances.
You can also use a browser protection tool (like the one built into Google Chrome) that alerts you if the website you own has been flagged for suspicious or malicious activity.
But it doesn’t have to be.
With the above information about phishing emails in mind, you’ll be well on your way to making your business's cyber security plan as airtight as possible.
Want to learn more web tips to keep you safe and improve your productivity online? This page has plenty of useful information.

Don’t trust your company’s critical data and operations to just anyone! This business advisory guide will arm you with 21 Revealing Questions you should ask any computer consultant before giving them access to your network.
7500 Jefferson St. NE
Albuquerque, NM 87109
505-823-3400