In today's digital landscape, law firms face unique challenges in maintaining security and efficiency.

Malvertising is a sneaky way for hackers to insert malicious code into on-line advertisements, infecting the computers of unsuspecting internet users. It is one of the newest ways to attempt to steal your personal information and to cause havoc inside
your computers. Now you may be asking yourself, what the heck is malicious code? It is any code that has been designed to have an effect unintended by the user. This malware, or malicious software, is hidden within online advertisements. It can be used by hackers to disrupt a computer's operation, gather sensitive information, or gain access to private computer systems. Malicious code effectively circumvents common antivirus software because the user "asks for it," but definitely gets more than he or she wanted. So, read keep reading to learn -What is Malvertising? What You Need To Know To Keep Safe.
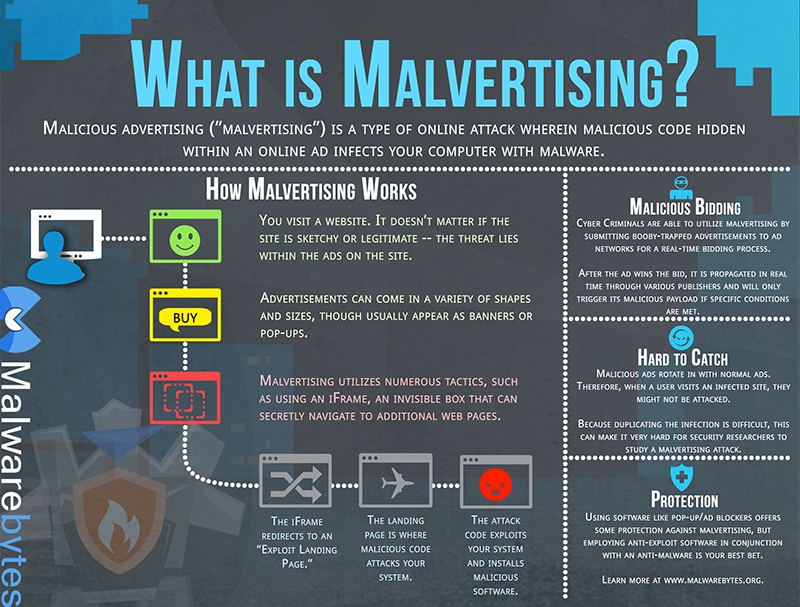
Malvertising is especially troublesome because it often is activated without any action being taken by the computer user. As a web page with the advertising is loading, the malware is quickly and quietly infecting the operating system. Most people are savvy enough that they know to be cautious about which web pages they choose to visit. Yet, malware is silently hiding even on the most trusted websites, such as Google, YouTube, and Rutgers. Site administrators are mostly unaware of the widespread corruption being piggybacked through their credible pages because third-party advertising agencies provide the promotional content. The ads are changed on a fast rotation, through an automated process, based on keywords entered by the user.
You can protect against malvertising infections by avoiding pop-ups that say you have won a prize for visiting their site, or ones that are offering freebies of money, products or discount coupons. Read the comments before you click to proceed with any downloads and always install the latest updates for your computer's operating system, installed software and browser plug-ins. Computer security anti-virus programs such as those offered by Norton and McAfee are always a good idea.
Signs that your computer might be infected include:
If you believe your computer security has been violated, you can start by running a scan using Microsoft's malicious software removal tool that came as part of your copy of Windows.
See also: Why Network Monitoring is Critical to Every Business Owner
Redirecting is an action that happens behind the scenes while you are surfing the Internet. and contributes to a hacker's ability to exploit their opportunities with malvertising. Whenever you type in a web address and land on the destination you request, dozens of other URLs are connecting with your computer for pop-ups, video files and other various functions to enhance your experience or make it more convenient and user-friendly. It is this process of redirection that makes hackers hard to trace and hard to avoid. Attempted attacks on your computer come indirectly through the other connected domains.

Don’t trust your company’s critical data and operations to just anyone! This business advisory guide will arm you with 21 Revealing Questions you should ask any computer consultant before giving them access to your network.
7500 Jefferson St. NE
Albuquerque, NM 87109
505-823-3400